So, I recently became a Podcast “junkie”, and a podcast recently brought up the Dark Web. But does the average person really understand what the Dark Web is, what can be found there, and the dangers there?
There are actually three levels to the Internet as we know it. There is the Internet that we think about –the Wikipedia pages, company websites, Facebook, LinkedIn, and results to our Google searches. This is what we call the World Wide Web and is where most of us lives online. This is also known as the “clear web”, and as big as all of the websites, and social media sites combined are, makes up only a tiny part of the Internet, according to The State of Cybersecurity article “What is the Dark Web?”
There is also a section we call the “Deep Web.” This level is where records and archives stored in the cloud live, and we can find them for the right price. We can find academic, medical, and legal records, scientific reports, subscriptions and conference information, and government resources. These items are not indexed, and the content includes anything behind a paywall or requires sign-in credentials. This is about 95% of the content which makes up the entire Internet.
If we go deeper, we can get to the third level of the Internet, known as the Dark Web. This is a hidden part of the internet where anonymity is the rule. Since everything is anonymous and no rules, it is the most nefarious level of the internet. This is where illegal information exists. You can find guns, drugs both prescription and recreational, sex trafficking, prostitution, and stolen goods on the Dark Web. Think of it as a giant “Dark eBay” where anything…and I do mean anything…you are looking for can be found. This should concern us as business owners. One of the most abundant and searched for items is information. If your system got breached and they could get 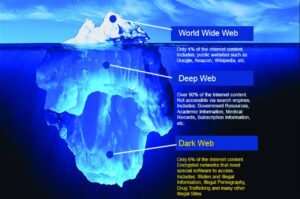
We mentioned before the Dark Web is like “Dark eBay” there are places there to buy credit card numbers, stolen subscriptions, hacked accounts and software. For example, a “lifetime” Netflix premium account goes for around $6. For about $500, you could buy the login credentials to a bank account with at least $50,000. Maybe you teach a course; it’s possible that a potential student could find the code to enroll within your course for free, or just purchase a whole new identity complete with social security number and passport.
The same article from The State of Cybersecurity, says there are several categories of tools or services that can present a risk to companies:
- Malware and virus Infection or attacks
- Keyloggers and remote access Trojans (RATs)
- Espionage
- Tutorials for support services
- Credentials for unacknowledged access
- Phishing
- Refunds
- Customer data
- Operational data
- Financial data
- Intellectual property/trade secrets
These risks can lead to the devaluing of a company by undermining the trust of the brand, doing reputation damage, or causing the company to lose ground to a competitor. They can also disrupt the company with malware, Distribute Denial of Service (DDoS) and ransomware attacks. The company could also be defrauded when IP theft or espionage causes direct financial loss.
Going back to that podcast I listened to last week, it gave the impression that the Dark Web was just out there and just anyone could be there, stumbling around and seeing things that aren’t appropriate. It planted the idea that our children could stumble onto these places. That is not the case. Your general Google, Bing, Yahoo or MSN web search engine is not going to suddenly dump you onto the Dark Web. There is an anonymizing browser called “TOR” that would allow access, but even with that browser you would have to jump through various IP addresses and proxy servers. It is also unpredictable, unreliable, and maddeningly slow – which is due to our law enforcement monitoring and catching the criminals and hackers.
Now that we have told you some of the bad things that can be found there, and how it can affect your business, lets switch gears and look at protecting your business.
Security is a process, not a product.
Just like there is no magic pill to lose that “Quarantine 20 lbs”, there is no single product that will magically protect your network. Your cyber security is the process of creating strong passwords, keeping those passwords secure, keeping your malware and anti-virus software up to date, using Firewalls and VPNs, and more. All these pieces work together to keep your network secure.
You need to have a CURRENT version of Windows or whatever operating systems you use.
Yes, sometimes it’s easy to ignore the update notifications. It seems like there is always a new one. Or maybe your previous version of Windows works just fine, so why should you spend the money to update? I get it. I understand the idea of “don’t fix what’s not broken.” But in this case, the older versions of Windows might not be “broken” but it might have security ‘leaks’ or doors. Many of the updates that come out for Windows or any software, have to do with security risks that were located, so they put out an update to close that door or plug a leak. Keeping the latest version and installing all the updates, keeps our network the most secure. If you are running Windows 7 or earlier version of Windows, it is no longer supported which means that there are no more updates to get, and any new vulnerabilities that are found will not be patched/fixed. So, you need to update immediately.
You NEED an Anti-Virus, preferably a Next-Gen AV that is monitored and maintained for you.
A Next-Generation Anti-virus takes traditional antivirus software to the next level, providing endpoint security protection. It goes beyond known file-based malware signatures and processes, by using a system-centric, cloud-based approach.
Firewall, with an active IDS/IPS subscription (Intrusion-detection/Intrusion Prevention Service)
This shouldn’t come as a surprise. Many of our blogs have mentioned a Firewall, especially the one Firewall 101, where we explained why they are important. The firewall puts that privacy fence around your house; even if you leave the front door open on a sunny day, no one is coming in without the proper key.
Backup! Best practice would be both a local, and an offsite copy
By backup, we are not talking “oh I am getting a new computer, so I should back up my hard drive”: we are talking about daily backups of the entire computer system. When you lose a hard drive or get attacked by a virus, at most, you will lose a single day’s work. These can be an external hard drive or cloud-based, or our personal favorite is Both! The reason we recommend both is most Ransomware attacks will encrypt attached hard drives as well, so if you are backing up to an external hard drive and think that you are safe, you may not be. When you go back to restore the data, if that has been encrypted just like your windows drive, then you “DON’T” have usable backup, but the cloud copy could still be used to restore your files.
Malware/Anti-Phishing email protection.
Good spam filters and anti-virus software will flag malware and phishing emails, but occasionally one will still sneak in. Good security training for your employees on how to identify these can make them more educated and less of a security risk. You can also use this time to discuss password security and other general Cybersecurity education.
I hope this overview of what the Dark Web is and how to protect yourself helps, but what happens if you are already there or affected? Tune in next blog where we will address just that.
At Techno Advantage, we want to have a Lunch & Learn, at your office or via Zoom, to educate your employees about the Dark Web and cyber security threats. We can also scan the Dark Web for your company or employees for compromised credentials Click this link and fill out the form and we can scour the dark web looking for your credentials, so you don’t have to: https://technoadvantage.com/darkwebscan/ or as always you can call for a personal consultation. (317) 857-0150




