We share all types of information on a regular basis, rather it’s our own information or that of our clients; often we share that information via email. But how secure is our email?
According to a paper “Why Should You Encrypt Email and What Happens if You Don’t” by Symantec, “roughly 95% of the contents that flows through corporate email systems consists of file attachments, making email the primary method for sharing files in most organizations.” That could mean medical, insurance, financial or other Personal Identification Information (PII) being passed around at an alarming rate, in plain text.
Encryption in Large Corporations vs. Small Businesses
Most large corporations use encryption software to secure files within their organization. Some industries have compliance requirements that set the level of encryption they must use. They protect the transmission of information within their organization as well as to outside recipients. But what about small businesses and individuals? You still need a secure way to transmit your personal and financial information safely.
Are Emails Really Secure?
We all know that emails can easily be intercepted and them being sent in clear text, this means they can easily be read by anyone who intercepts them. Often, we overestimate how secure our emails are. Afterall, we must use a password to retrieve our emails, so that means they’re secure, right?
Risks of Cloud-Based Information Storage
But it’s more than just sending information via emails, we store personal and financial information in cloud-based software, such as Google Docs, Dropbox, Trello, and many others. Recently, the Naked Security by Sophos published an article entitled “Trello Exposed! Search Turns Up Huge Trove of Private Data”. The weakness identified was not in the Trello software, but rather that people were storing financial and personal information without taking proper precautions to secure the data. In this case, people set the Trello board to public, which allowed internet searches to find the information.
What Can Individuals Do?
So, as an Individual, what can I do? Say I need to send a payment authorization form. How can I protect my credit card information but still get this form submitted? Here are some solutions to help that do not require additional software.
Encryption or Password Protection for PDFs
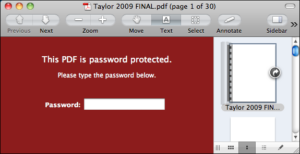
When sending a PDF file using Acrobat Reader or other versions:
- Open the file in Acrobat Reader or other version
- Choose “Tools” > “Protect.”
- Select to encrypt the file with a password.
- Set password as desired. Click “OK” and then click “Save.”
- Email the encrypted file.
- Call or text the person receiving the encrypted file and give them the password. It will be case sensitive.
Protecting Excel or Word Files

How about your Excel or Word files? Those files types, as well as any of Office suite can easily be password protected. This is a great way to keep your information protected. Just make sure you remember the password!
- Open the file within the Excel.
- Choose “File” > “Info”.
- Choose “Protect Workbook”
- Select Encrypt with Password. The password is case sensitive and will be required every time the file is opened.
- Set a password as desired. Click “OK” and then click “Save”.
If you have an Office 365 subscription and want to use encryption, you will need to purchase an add-on to the standard subscription. This add-on cost $2/month for each Office 365 user.
Sending Encrypted Emails with Outlook
If you need a more secure solution for transmitting, Microsoft Outlook allow you to send encrypted emails. This option does require a Digital ID.
What Is a Digital ID?
You can write and send these messages the same as any other messages, but they do require you to have a Digital ID and the recipients must have your Digital ID to view the message.
So first, you need a Digital ID. But what exactly is this Digital ID?
Digital IDs, also known as digital certificates, is a validate process to ensure your identity and help protect messages by giving a unique code to your messages, called a digital signature. This ensures that you are sending the message, not an imposer and that the contents have not been altered in transit.
How to Get and Use a Digital ID in Outlook
To get your own digital ID and set it to be used with Outlook:
- Get a digital ID from a certifying authority. You will need to obtain a digital ID issued by an independent certification authority. There are two main authority for this GlobalSign or IdenTrust.
- Specify the digital ID to use by going into Outlook.
- “File” > “Options” > “Trust Center”.
- Under Microsoft Outlook Trust Center, click “Trust Center Settings”.
- Select E-mail Security > “Encrypted email” > “Settings”.
- Under Security Settings Preferences, click
- In the Security Settings Name box, enter a name.
- In the Cryptography Format list, click S/MIME. Depending on your certificate type, you can choose Exchange Security instead.
- Next to the Signing Certificate box, click to Choose and then select a certificate that is valid for digital signing.
- Select the Send these certificates with signed messages check box unless you’re be sending and receiving signed messages only within your organization.
- Add a recipient’s digital ID to your contacts:
- Open a message that is digitally signed as indicated in the message by the Signature icon.
- Right click the name in the From box, and then click Add to Outlook Contacts.
- If you already have an entry for this person, in the Duplicate Contact Detected dialog box, select Update information of selected Contact.
- On the Navigation bar, click People.
- On the Home tab, click List.
- Double-click the person’s name, and then on the Contact tab, click Certificates.
To encrypt a single message:
- In message that you are composing, click File> Properties.
- Click Security Settings, and then select the Encrypt message contents and attachmentscheck box.
- Compose your message, then click Send.
To encrypt all outgoing messages by default:
- On the File choose Options>Trust Center > Trust Center Settings.
- On the Email Securitytab, under Encrypted email, select the Encrypt contents and attachments for outgoing messages check box.
- To change additional settings, such as choosing a specific certificate to use, click Settings.
Within the Settings, you can also make it so the email can’t be forwarded. If you haven’t checked into the various options, you should see what you can lock down.
Final Thoughts
Techno Advantage hope that these tips and instructions help you with your security concerns, but if your small or medium sized business need a more advanced solution, reach out today to schedule a consultation with one of our trusted technicians. Let us do a cyber security assessment of your current system and work with you to find the right solution to protect you and your clients.
Author
-

Jay S. Allen, MCP, MCSA, MCSE, MCSE+ Security, is an experienced IT professional with more than 20 years in the industry. He specializes in delivering enterprise-level cybersecurity and IT support solutions tailored to small and mid-sized businesses. Through Techno Advantage, Jay is dedicated to helping organizations strengthen their security posture and achieve greater efficiency through smart, scalable technology solutions.